Why is NIS2 being transposed in Portugal?
The transposition of Directive (EU) 2022/2555, better known as NIS2, represents a paradigm shift in the way Portugal approaches cybersecurity. Decree-Law No. 125/2025 was published on 4 December 2025 and comes into force 120 days after that date, i.e. on 3 April 2026. The measure aims to address the rise in attacks on critical infrastructure and harmonise practices across Member States, creating a single, mandatory national cybersecurity framework. The legislation repeals Law No. 46/2018 and Decree-Law No. 65/2021 and introduces the Legal Framework for Cyberspace Security, with new requirements for risk management, incident reporting and supervision. For organisations involved in the technical management of buildings and OT networks, such as those using SACE systems and automation platforms, NIS2 provides a more structured framework and requires a rethink of security processes and policies.
Quem está abrangido pelo Regime Jurídico da Segurança do Ciberespaço
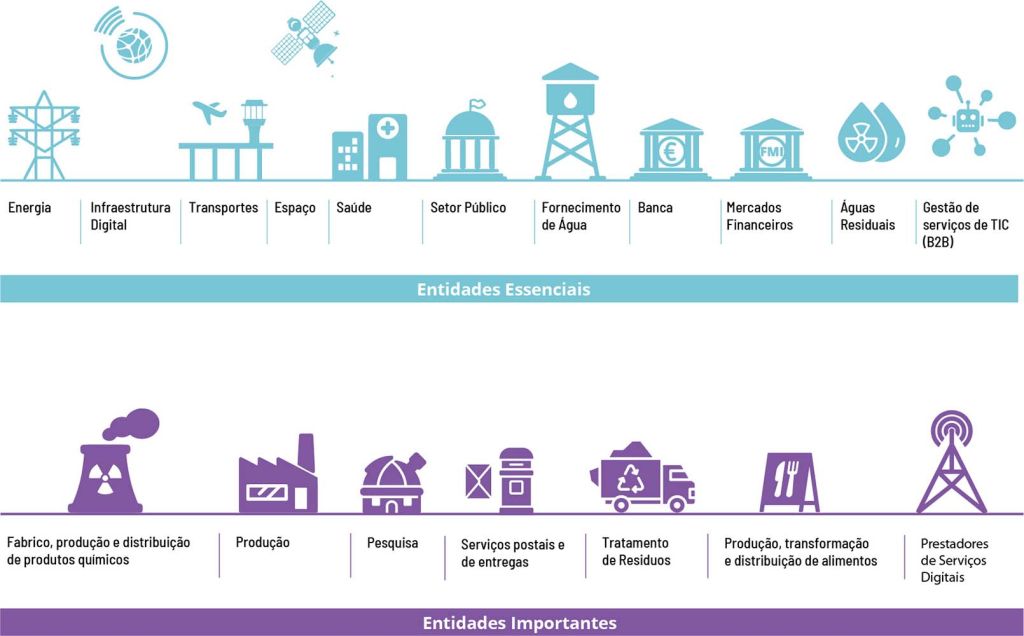
The Cybersecurity Legal Framework applies to three categories of entities: essential, important and relevant public entities. Essential entities encompass operators in critical sectors such as energy, transport, healthcare, water supply, banking, telecommunications and digital infrastructure; they also include qualified trust service providers, domain registries and companies providing public electronic communications networks. Important entities are organisations in the same sectors, but of a smaller size or with lower risk exposure, which do not meet the criteria for essential entities and which warrant classification based on their vulnerability or potential impact. Relevant public entities include public administration bodies with a high level of digital integration or critical missions, grouped into two categories according to size and criticality. It should be noted that micro and small enterprises are, as a rule, excluded from the regime, except where they provide essential services or are unique in the supply chain, which reinforces the proportionality of the obligations.
In the context of smart buildings, energy operators, healthcare facilities and digital infrastructure that use SACE systems may qualify as essential entities. Suppliers of sensors, software and technical services may be classified as important entities if they contribute to the operation of these systems. These classifications determine the level of supervision (proactive for essential entities and reactive for important entities) and the amount of fines in the event of non-compliance: up to €10 million or 2% of global turnover for essential entities and up to €7 million or 1.4% for important entities.

Obligations and responsibilities: risk management, supply chain and incidents
NIS2 places responsibility for cybersecurity with management bodies. These bodies must approve risk management measures, oversee their implementation and ensure that regular cybersecurity training is provided. Essential and important entities are now required to implement a structured risk management system covering various areas: incident handling, business continuity, supply chain security, security in the procurement, development and maintenance of network and information systems, continuous assessment of the effectiveness of measures, basic cyber hygiene practices and training, encryption policies, human resources security and multi-factor authentication
Supply chain security is a key innovation for building operators. Organisations should assess the vulnerability of each supplier and service provider, the overall security quality of products, secure development practices and, where necessary, apply restrictions on the use, transfer or disposal of equipment. For SACE systems, this means reviewing contracts, verifying that equipment and software manufacturers meet cybersecurity criteria, and ensuring that remote connections and interfaces are protected.
Incident reporting is also strict: organisations must submit an initial alert to the CNCS (National Cybersecurity Centre) within 24 hours of detecting a significant incident, send a detailed update within 72 hours, and submit a final report within 30 working days. The same incident must be reported to potentially affected users. In addition, essential and important organisations are required to maintain an annual report on the state of cybersecurity and to submit this information to the CNCS. They must also appoint a cybersecurity officer and a permanent point of contact with the CNCS. These obligations require building technical teams to coordinate closely with IT departments and senior management.
Incident reporting is also strict: organisations must submit an initial alert to the CNCS (National Cybersecurity Centre) within 24 hours of detecting a significant incident, send a detailed update within 72 hours, and submit a final report within 30 working days.
Deadlines, transition and penalties
Decree-Law No. 125/2025 comes into force on 3 April 2026, but some provisions will only become mandatory once the CNCS has approved the implementing regulations – a process that may take up to 24 months following the publication of the legislation. Until then, entities must register on an electronic platform and update their information every two years. New entities will have 30 days to register; those already operating will have 60 days from the platform becoming available.
The penalty regime has been tightened: critical entities may be fined up to €10 million or 2% of their global turnover, whilst significant entities face fines of up to €7 million or 1.4%. Failure to report incidents, failure to implement security measures or obstruction of audits may trigger these fines, and the authority may also impose precautionary measures, such as the suspension of operations or the replacement of those responsible. The existence of grace periods – fines deferred for one year for organisations that are adapting – does not diminish the urgency of starting the compliance process immediately.
Another key point is the general exclusion of micro and small enterprises, except where they provide essential services or are critical suppliers. This exclusion reinforces the proportionality of the regime but requires large operators to be mindful of the vulnerabilities that small partners may introduce.
Impact on the technical management of buildings and BMS/OT systems
For operators and integrators of building management systems, the new regulatory framework is more than just a legal formality. NIS2 might designate BMSs as critical cybersecurity components, necessitating a review of network architectures, hardware, software and operational practices. As many facilities integrate HVAC, energy, physical security and remote access systems, the risk of attack increases. The new regime requires these platforms to be designed with security by default: end-to-end encryption, robust authentication controls and OT network segmentation.
From a supply chain perspective, BMS integrators and manufacturers must provide cybersecurity documentation and evidence of compliance, and building operators will need to audit the security of sensors, actuators, gateways and software. The appointment of a cybersecurity officer brings maintenance teams and management closer together, strengthening accountability. The annual report and reporting deadlines mean that technical management teams must collect and record security metrics, in addition to operational indicators.
Although the preparation is demanding, the new regime also creates opportunities: by aligning themselves with European standards, companies increase the resilience of buildings, reduce the risk of disruptions and can gain a competitive advantage. For WiseBuilding, which develops automation and SACE solutions, taking a proactive stance in implementing NIS2 requirements strengthens customer confidence and paves the way for differentiated services in risk management, consultancy, monitoring and infrastructure modernisation.
Conclusion
The transposition of NIS2 via Decree-Law No. 125/2025 raises the bar for cybersecurity in Portugal and introduces clear obligations for organisations operating in critical sectors. For the world of smart buildings and BMS solutions, the new regime is not merely a legal formality; it is a call to integrate cybersecurity into planning and day-to-day operations. Identifying entities, managing risk, monitoring the supply chain and ensuring a rapid response to incidents are becoming essential factors in protecting people, assets and data. By adapting early and rigorously, WiseBuilding can turn this requirement into a competitive advantage, offering safer and more reliable solutions in an increasingly demanding market.
WiseBuilding® is technically capable of implementing any project that creates buildings that think, save and protect the planet. Consult us.
WISEFRAMEWORK is a BACnet B-AWS certified software solution for state-of-the-art integration, control, management and visualisation in building automation systems. Designed to redefine the way buildings are operated through an open platform and seamless harmonisation between building-generated data by supporting multiple protocols including BACnet, Modbus, KNX, OPC-UA and MQTT. Through the use of Haystack technology, the software also empowers the building for the future at the forefront in the integration of the various technical systems.



